TL;DR – WhatsApp uses the Signal Protocol X3DH along with the Double Ratchet algorithm to provide end-to-end encryption for messages. Only you and the person you’re chatting with can read them. However, E2EE only protects message content. Metadata, spyware, backups, and unlocked apps can still expose your privacy. That’s why using app locks, encrypted backups, and trusted platforms like Signal matters. Privacy isn’t a luxury but a digital necessity.
A few months ago, on a vacation in the Caribbean, I was sitting at a beach café on a lazy afternoon. With a Piña Colada sweating on my table and my phone in my hand, I was scrolling through TikTok. Suddenly, I came across a video of a golden retriever chasing its tail without stopping. Hey, this is something my close friend Scott would love. Scott was in Dubai at that time attending a business conference. I shared it with him on WhatsApp. Moments later I get a reply “That dog’s so funny 🤣…”
Now this got me thinking. I, sitting in the Caribbean, sending a message to him in Dubai. Obviously, it would have travelled through many data centers, servers and other networks just to reach him. So how secure was my message? During transit, could anyone intercept and read it?
Well thanks to end-to-end encryption (E2EE) that doesn’t happen.
What’s end-to-end encryption (E2EE)?
E2EE ensures that our messages are never read by any middlemen. All encryptions and decryption happen on our devices, ensuring privacy.
Imagine there are two friends, Rick and Tom. Each friend has a public key (that they can share with each other) and a private key (that they always keep on their phone).
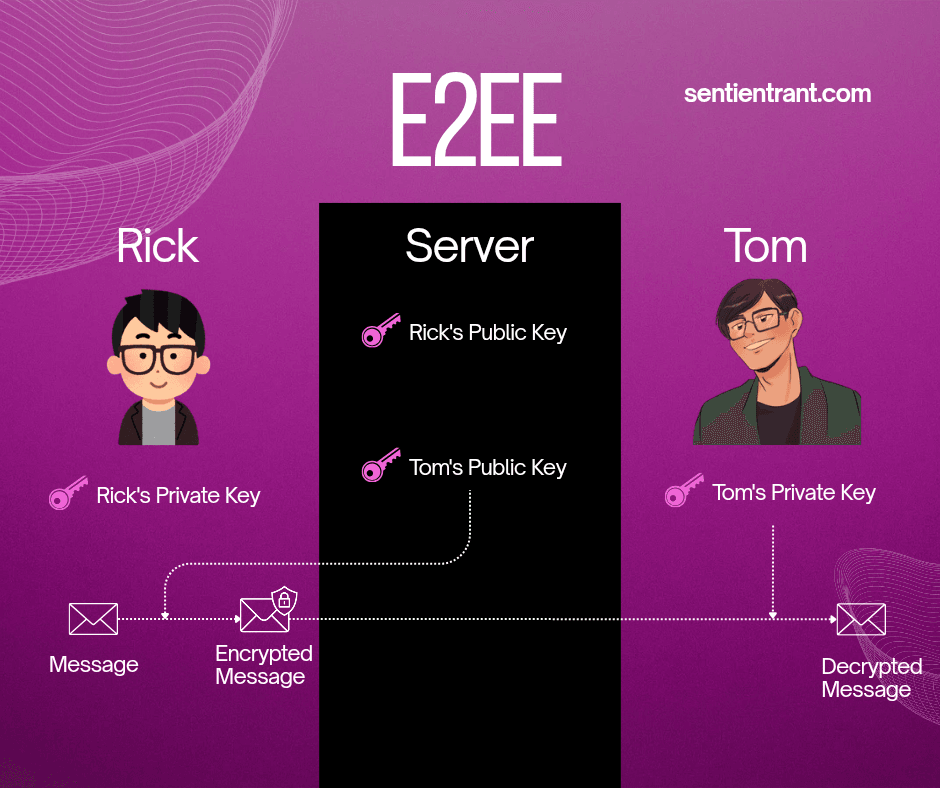
Now, when Rick sends a message to Tom, the app locks the message first with Tom’s public key. Only Tom’s private key can open it. Even Rick himself can’t open it after it’s locked. Then it is sent across. Message travels through the company’s networks and servers before it reaches Tom. Upon receiving, the app opens Rick’s message using Tom’s private key. Now Tom can read it.
Only the public keys are shared with each other. These can only be used to lock the messages. Private keys can only open them. They remain on each other’s respective devices, ensuring that the messages remain private. Isn’t it genius? As long as your device isn’t compromised, your messages will truly remain private. This is the simplified gist of how the end-to-end encryption (E2EE) works.
The Signal protocol
The Signal Protocol is a modern encryption system that powers secure messaging in apps like WhatsApp, Signal, and Messenger. It combines two powerful techniques – X3DH (Extended Triple Diffie-Hellman), for creating a shared secret key and the Double Ratchet algorithm for constantly changing keys after every message.
WhatsApp and Signal take E2EE to the next level by using the Signal protocol. Well, to explain this, let’s use our two old friends, Tom and Rick.
Step 1 :- The setup
Contrary to the explanation i gave earlier about E2EE where each user had just 1 keypair, the reality is different. Each user (Tom and Rick) has different key pairs (public and private key).
- An identity key pair – Created when the app is installed. Used to verify the person
- Signed pre-key pair – Helps someone start a session with you even if you are offline. Usually replaced in a few weeks or months.
- One time pre-key pair – These are used for one time use and are discarded after each use. These are also used optionally (if present) in case someone wants to start a chat while you are offline to give a more added security.
- Temporary/Ephemeral key pairs – Each user also generates temporary key pairs during each operation. After these are used, they are disposed of, as well.
So, all the private halves of all key pairs are stored on the user’s device and the public halves of all key pairs are stored on the server.
Step 2 :- X3DH – The first handshake
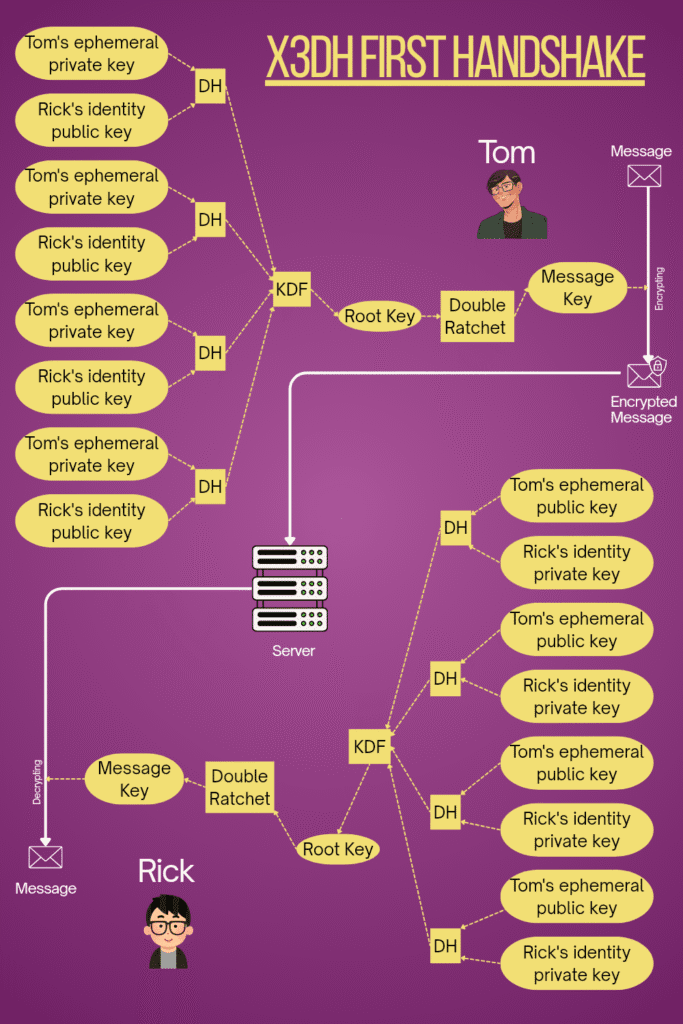
Imagine, Tom wants to send a message to Rick for the very first time.
Tom takes public versions of Rick’s identity key, Rick’s signed pre key and Rick’s one time prekey (if present) from the server.
He then does DH operations as given below.
- Tom’s ephemeral private key with Rick’s identity public key
- Tom’s ephemeral private key with Rick’s signed public pre-key
- Tom’s identity private key with Rick’s signed public pre-key
- Tom’s ephemeral private key with Rick’s one-time public pre-key (optional)
What’s DH (Diffie-Hellman) operation?
A DH (Diffie-Hellman) operation is like a smart math trick that lets two people create the same shared secret without actually sending it to each other.
Tom mixes one of his private key with Rick’s public key. Rick later mixes the similar private key of his with Tom’s public key.
Even though they never share their private keys with each other, both end up with an identical secret key.
The results obtained are like different ingredients. They are combined and processed by the KDF algorithm to generate the initial root key. This root key is used for double ratcheting to derive the message key. This message key is used to encrypt the message.
What’s KDF (Key Derivation Function)?
A KDF (Key Derivation Function) is like a recipe that takes those secret ingredients and turns them into specific keys for encryption and authentication.
It ensures that even if one part is guessed or reused, the final keys stay secure and unique each time.
Tom’s ephemeral public key is also added to the header of the message with other details. It is then sent to Rick. Rick, upon receiving the message, performs the same operations to generate the message key and decrypts decrypts the message.
Now Rick and Tom have a shared root key without actually having to physically share the key among themselves. This is the purpose of the X3DH. Both users end up with the same root key through multiple mixes without anyone else getting to know about it.
After this, all consumed one time pre-keys and ephemeral keys are deleted.
Step 3:- Double Ratchet
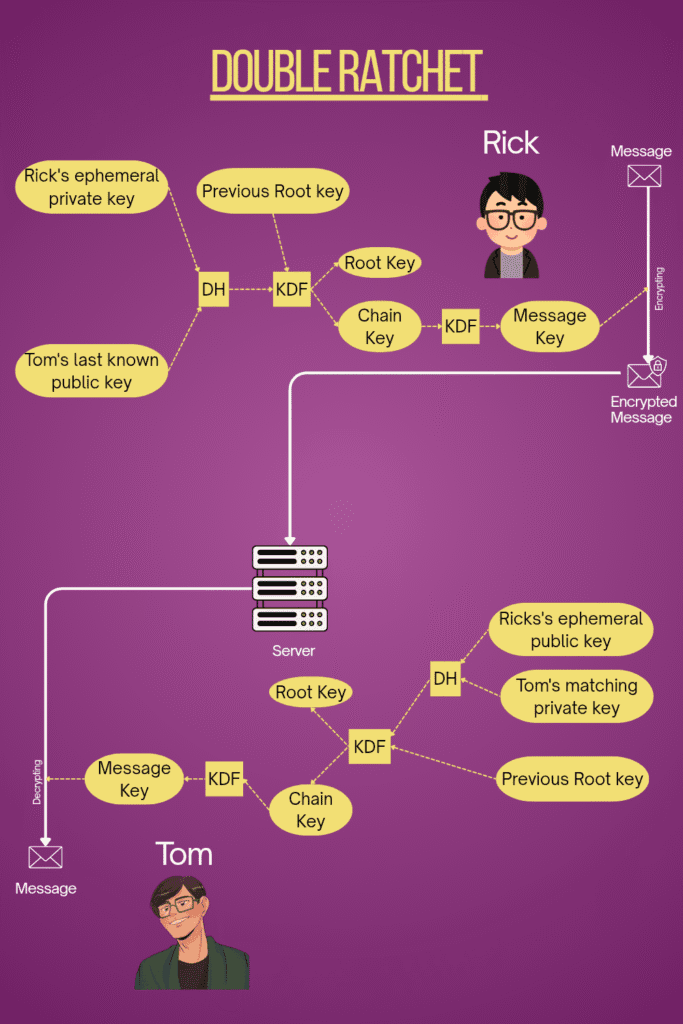
Now that the connection is established, Rick decides to reply to Tom. For that, he first creates a new set of ephemeral keys (private and public). He performs DH operations on his newly created ephemeral private key with Tom’s last known public key from the previous message. Then, the DH output and the existing root key is passed through a KDF function to create the new root key and a new chain key. This process is called DH ratcheting.
Now the generated chain key is passed through a one-way KDF function to create a new message key and a new chain key. This ratcheting is called symmetric ratcheting.
This created message key is used to encrypt the message. Rick’s new public key is also attached in the message header and sent to Tom.
Tom does the same steps done by Rick with his own private key and Rick’s public key he sent with the message and arrives at the message key. The message is then decrypted with this key. After this, the unnecessary keys are deleted and only necessary keys are kept for future messages.
Even if some hackers somehow manages to hack one of the phones and obtain all the keys at that particular instant. They can only read that particular message. They can’t read the future messages because all the keys change during the next DH ratcheting ie., when the other person replies. Since during symmetric ratcheting, the KDF is used in one-way fashion, having a later chain key cannot derive the previous chain keys. As a result, the hackers can’t read the previous messages.
Both these mechanisms work together to make double ratcheting work.
How truly are you protected by end-to-end encryption (E2EE)?
End-to-end encryption keeps our chats safe on the move, but our metadata, backups, and unlocked apps can still expose us.
E2EE protects our messages while in transit. Without encryption, our internet providers, network admins, company executives etc. could read our private messages.
But is it really enough? Well apparently not.
1) Even if our messages are encrypted in transit, nothing protects our metadata
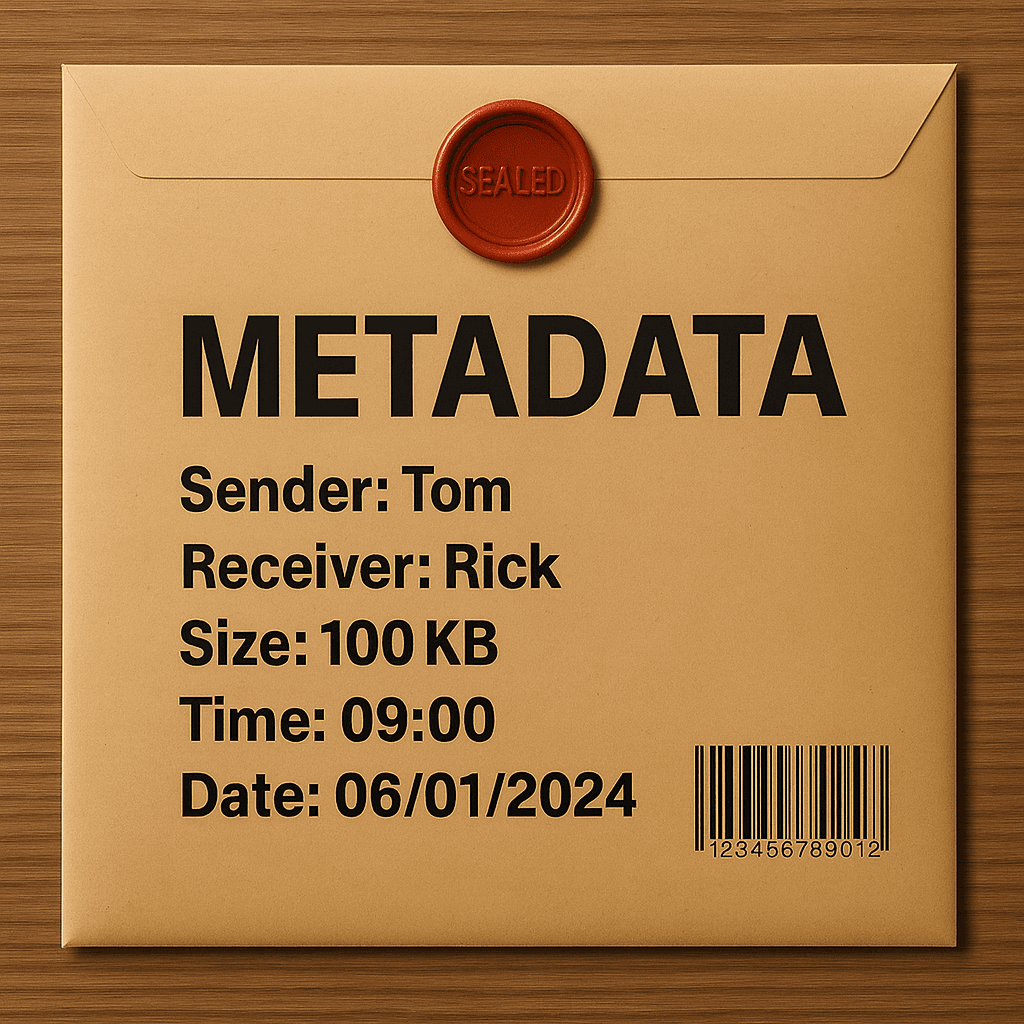
Our metadata is accessible by companies and others. Metadata includes phone number/id of the sender and receiver, when the message was sent, message size etc. By analysing this data, anyone can figure out who we chat with, the duration and frequency of our chat and believe you me, they can even guess the contents of our message without actually reading it. WhatsApp admits it collects metadata and passes it on to Meta only for service links and analytics. Currently, Signal claims to collect the least metadata just to function. So if you really want to keep your metadata more private, Signal might be a better choice.
2) Spyware and malware compromise privacy

Keeping your phone free from trojans and viruses is important. If your mobile is infected with spyware, then when you open your messaging app, all your messages will be visible to the hackers. Update the OS and apps regularly. Only download apps from official stores like Google Play Store or Apple App Store.
3) Privacy becomes a joke if your app is easily accessible
If a person steals or hacks your phone, they can easily open your app if your app isn’t locked. So if you want to maintain your privacy, be sure to enable the app lock on your messaging app. This way, it becomes difficult or rather impossible for anyone other than you to access.
4) Why go after the messages if they could go after your backup
All that privacy doesn’t matter if the hackers or scammers can just get your information from your backup. Signal provides encrypted local backup by default. WhatsApp also provides encrypted backups, but users must enable them manually as they are not enabled by default.
Why end-to-end encryption matters
Privacy isn’t a luxury but a necessity.
There are many in the world who value privacy. But governments around the world don’t like encryption. They argue that it will be used by terrorists to communicate securely with each other. Well it is true, but isn’t that the same for any technology. Good people and bad people can use the same technology but it doesn’t mean no one should use it.
Many claim that they have nothing to hide, so why fear government tracking.
Just imagine a couple having a very private conversation about starting a family. They are discussing pros and cons, whether they are financially secure or emotionally mature etc. There is nothing scandalous or wrong with this discussion, only that it’s a private one. Just imagine there’s someone else in the room quietly observing the conversation. Isn’t that just creepy? I mean, whoever it is.
Privacy isn’t a luxury but a necessity. We should value it especially when we are using the digital space because we can’t see the creeps who observe – who they are, what their agenda is and how our information is used.
E2EE is an amazing technology that ensures that our messages, calls and other activities are safe from external creepy surveillance. Just like we close our doors to have a private conversation in the physical world, E2EE does the same in our digital world.
FAQs
End-to-end encryption ensures that only the sender and receiver can read a message. The message is locked on your phone and unlocked only on the recipient’s phone — no one in between (not even the company or hackers) can see it.
Imagine two friends — one locks a message with the other’s public key. Only the receiver’s private key can unlock it. The private keys never leave the devices, keeping the conversation private as it travels through servers and networks.
The Signal Protocol is an advanced encryption system used by Signal and WhatsApp. It combines X3DH (Extended Triple Diffie-Hellman) to establish a secure connection and the Double Ratchet algorithm to keep changing keys after every message. Even if one message key is compromised, all past and future messages remain safe.
X3DH is the first step of the Signal Protocol — it’s how two users securely establish a shared secret key even if they’ve never talked before. It combines multiple Diffie-Hellman (DH) key exchanges between different types of key pairs (identity, signed pre-key, and one-time pre-key) to create a common secret without ever actually sending it across the network. In simple terms, X3DH makes sure that when you start a new chat, both you and your contact have a matching encryption key that no one else — not even the server — knows.
The Double Ratchet algorithm constantly refreshes encryption keys for every new message. This means that even if someone gets access to one message, they cannot read previous or future ones.
Not entirely. E2EE protects message content, but metadata (like who you chat with, when, and how often) can still be visible to the service provider. Other privacy threats like spyware, unencrypted backups, or unlocked apps can also expose data.
Metadata includes your phone number, chat frequency, time, and message size. By analysing metadata, others can infer who you talk to and how often — even without reading your messages.
Use app locks for your messaging apps. Enable encrypted backups. Keep your phone and apps updated. Avoid installing apps from untrusted sources.
Some governments argue that encryption hides criminal or terrorist communication. However, like any technology, it can be used for both good and bad. Restricting it would compromise everyone’s digital privacy.
Privacy isn’t about hiding — it’s about control. Even ordinary conversations (like a couple discussing starting a family) deserve privacy from unwanted observation.
Both Signal and WhatsApp use the Signal Protocol for end-to-end encryption, meaning message contents are private even from the companies themselves. The main difference lies in data handling: Signal collects almost no metadata—only your phone number, account creation date, and last connection time (rounded to a day)—while WhatsApp gathers and shares more metadata with Meta, including contacts, device info, and usage data. Signal also leads in future-proofing encryption. It has introduced the Sparse Post-Quantum Ratchet (SPQR), designed to resist attacks from powerful quantum computers that could break traditional cryptography. WhatsApp has not yet implemented similar post-quantum protections. In short, both apps secure your chats, but Signal provides stronger privacy, less data collection, and more advanced encryption safeguards.
Feedback
Your feedback helps improve future articles. If you found this post useful or have suggestions, you can share your thoughts anonymously. A quick rating would be appreciated
Your feedback has been sent
Subscribe to our newsletter
Want the best of Sentient Rant without checking the site every day? Get a monthly digest of our tech blog posts —one email, once a month, zero clutter.
Check out our posts
How VPNs really work: Protocols, safety and myth
Passkeys Explained: The End of Passwords or Just Another Tech Gimmick?
The real cost of free apps
183 Million Gmail addresses in a data leak — Here’s what actually happened (and what you should do)
Brain-computer interfaces (BCI) : The next upgrade
DNA data storage: Replacing hard drives with DNA
Hard drives fade. DNA endures. Discover how scientists are turning life’s own code into the…









Very comprehensive post on signal protocol
Thank you
I think, that you are mistaken. Let’s discuss.
_ _ _ _ _ _ _ _
https://automietenmarbella.de
Yes sure. I would love to. Do share your concerns to sentientrant@gmail.com. thank you.